The following guide will show you how to correctly change your Network Card’s MAC Address using the Windows Registry. Below are several different methods to accomplishing this and I am sure that one will work for you. These methods can be used in both Windows Vista and Windows 7; I have not yet tested them in the Windows 8 environment.
Method One:
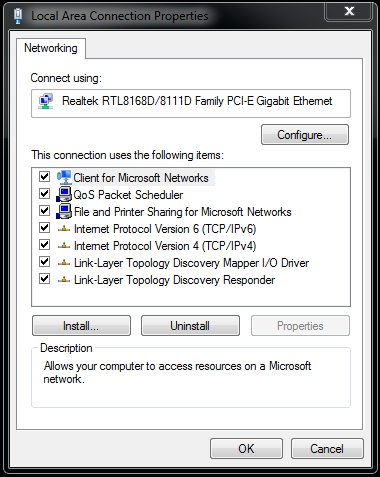
1. Access your network connection properties and select the configure option.
2. Select the Advanced Tab and then select Network Address. From here you need change the Value to custom and enter your desired MAC Address. Remember that this can only be twelve numbers in length.





